UPDATES LOG
(UPDATED ON 02-MAY-2022)
Please make sure you keep your applications up to date, will be updating this page once a new update has been issued.
Windows Application - Version 1.0.20 released on 02-MAY-2022
• The H+TCP and S+TCP have been updated and are now running on version 3, this is to increase efforts with the unblocking of ISP and Governments from the use of VPN
• All older version will stop working with H+TCP and S+TCP mode, please update your application to continue using these modes.
• Overall enhancements to make it run smoothly and bug free.
Windows Application - Version 1.0.19 released on 31-JUL-2021
• The H+TCP Mode has now been fixed and also gotten a sucessful update, this is to increase efforts with the unblocking of ISP and Governments from the use of VPN
• Overall enhancements to make it run smoothly and bug free.
Windows Application - Version 1.0.18 released on 12-JUL-2021
• The S+TCP Mode is now S+TCP2 after a sucessful update to version 2, this is to increase efforts with the unblocking of ISP and Governments from the use of VPN
• Overall enhancements to make it run smoothly and bug free.
Windows Application - Version 1.0.17 released on 14-JUN-2021
• The S+TCP Mode has been upgraded and implemented with new features, to help with the unblocking of ISP and Governments from the use of VPN
• Overall enhancements to make it run smoothly and bug free.
Windows Application - Version 1.0.16 Patch Updates released on 02-Apr-2021
• Improved S+TCP mode, previous versions will no longer work with S+TCP mode, Please kindly update to the newest version to use it
• Overall enhancements to make it run smoothly and bug free.
Windows Application - Version 1.0.16 released on 14-JUN-2020
• This is primarily a maintenance release with bugfixes and improvements. This release also fixes a security issue (CVE-2020-11810, trac #1272) which allows disrupting service of a freshly connected client that has not yet not negotiated session keys. The vulnerability cannot be used to inject or steal VPN traffic.
• A list of changes is available here
• Please note that LibreSSL is not a supported crypto backend. We accept patches and we do test on OpenBSD 6.0 which comes with LibreSSL, but if newer versions of LibreSSL break API compatibility we do not take responsibility to fix that.
• Also note that Windows installers have been built with NSIS version that has been patched against several NSIS installer code execution and privilege escalation problems. Based on our testing, though, older Windows versions such as Windows 7 might not benefit from these fixes. We thus strongly encourage you to always move NSIS installers to a non-user-writeable location before running them. We are moving to MSI installers in OpenVPN 2.5, but OpenVPN 2.4.x will remain NSIS-only.
• Compared to OpenVPN 2.3 this is a major update with a large number of new features, improvements and fixes. Some of the major features are AEAD (GCM) cipher and Elliptic Curve DH key exchange support, improved IPv4/IPv6 dual stack support and more seamless connection migration when client's IP address changes (Peer-ID). Also, the new --tls-crypt feature can be used to increase users' connection privacy.
Android Application - Version 1.0 released on 5-March-2019
• Easy to use interface
• Get connected in seconds
• Complete Anonymity
Windows Application - Version 1.0.15 Beta released on 02-Apr-2019
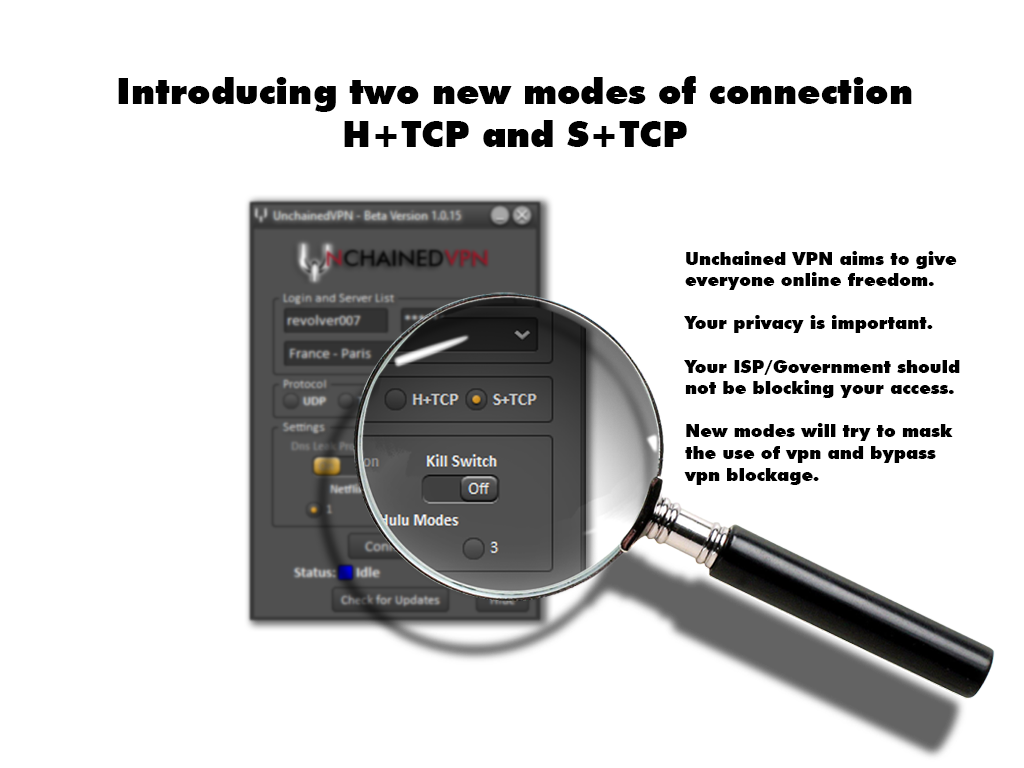
• Added two new modes of connection, H+TCP and S+TCP
• Overall enhancements to make it run smoothly and bug free.